Analyzing a real-world unsigned integer wrap to stack buffer overflow C vulnerability
What is an Integer Overflow Vulnerability? | Hacking 101Подробнее
Vulns1001 06 IntegerOverflow CVE-2019-14192🌐🗄3️⃣ 02 ACID FlowПодробнее

Running a Buffer Overflow Attack - ComputerphileПодробнее

Buffer OverflowПодробнее

Integer/ Buffer Overflow Vulnerability - Real World ExampleПодробнее

Stack Buffer Overflows - a primer on smashing the stack using CVE-2017-11882Подробнее
how do hackers exploit buffers that are too small?Подробнее

How to exploit a buffer overflow vulnerability - PracticalПодробнее

Software Security: Vulnerabilities - Integer/Buffer OverflowПодробнее
buffer overflow bypass ASLR and DEP with ROP ChainПодробнее

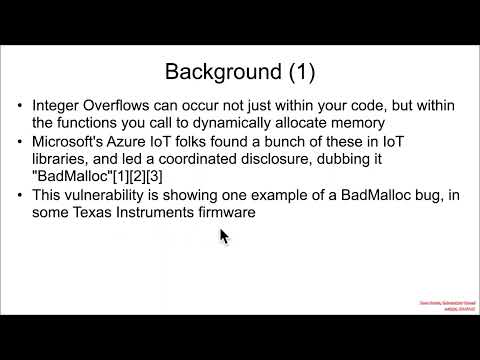
Vulns1001 06 IntegerOverflow CVE-2021-22636🧪🥱➡🤢🔜🤮 01 Background FTFПодробнее
why do hackers love strings?Подробнее

Buffer Overflow P20 | Integer Overflow | CTF WalkthroughПодробнее

Stack Buffer Overflow exampleПодробнее

Binary Exploitation Basics - Integer Limits & gets() Buffer OverflowПодробнее

Buffer, Stack and Integer OverflowПодробнее